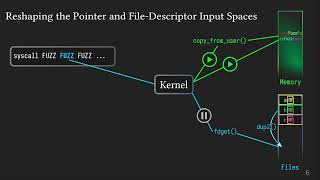
ndss 2024 - syzbridge: bridging the gap in exploitability assessment of linux kernel bugs in the lin
Published 3 months ago • 40 plays • Length 20:39Download video MP4
Download video MP3
Similar videos
-
 14:56
14:56
ndss 2022 progressive scrutiny: incremental detection of ubi bugs in the linux kernel
-
 15:25
15:25
ndss 2024 - enclavefuzz: finding vulnerabilities in sgx applications
-
 24:04
24:04
ndss 2024 - k-leak: towards automating the generation of multi-step infoleak exploits against the li
-
 20:43
20:43
ndss 2024 - degpt: optimizing decompiler output with llm
-
 19:17
19:17
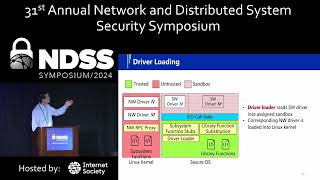
ndss 2024 - ldr: secure and efficient linux driver runtime for embedded tee systems
-
 14:53
14:53
ndss 2022 an in-depth analysis of duplicated linux kernel bug reports
-
 18:22
18:22
ndss 2024 - file hijacking vulnerability: the elephant in the room
-
 7:10
7:10
install nessus scanner on linux 2024 | best easy way | cyber shadow |
-
 20:53
20:53
tenable vulnerability management | installing nessus scanners and nessus agents on ubuntu linux
-
 18:21
18:21
give me 15 minutes and i'll change your view of linux tracing
-
 21:22
21:22
ndss 2024 - mock: optimizing kernel fuzzing mutation with context-aware dependency
-
 19:35
19:35
ndss 2024 - larmix: latency-aware routing in mix networks
-
 22:17
22:17
ndss 2024 - replicawatcher: training-less anomaly detection in containerized microservices
-
 22:26
22:26
ndss 2023 - no grammar, no problem: towards fuzzing the linux kernel without system-call descript...
-
 19:45
19:45
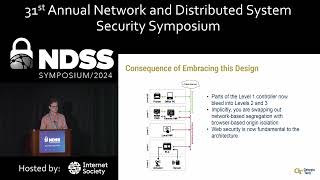
ndss 2024 - compromising industrial processes using web-based programmable logic controller malware
-
 14:05
14:05
ndss 2021 detecting kernel memory leaks in specialized modules with ownership reasoning
-
 19:11
19:11
ndss 2024 - beyond the surface: uncovering the unprotected components of android against overlay att
-
 25:15
25:15
ndss 2024 - phoenix: surviving unpatched vulnerabilities via accurate and efficient filtering of sys
-
 20:56
20:56
ndss 2024 - faster and better: detecting vulnerabilities in linux-based iot firmware with optimized
-
 12:15
12:15
ndss 2022 preventing kernel hacks with hakcs
-
 15:24
15:24
ndss 2024 - parrot-trained adversarial examples: pushing the practicality of black-box audio attacks