obfuscation from noisy linear fe
Published Streamed 4 years ago • 353 plays • Length 1:04:57Download video MP4
Download video MP3
Similar videos
-
 25:11
25:11
indistinguishability obfuscation without maps: attacks and fixes for noisy linear fe
-
 1:04:00
1:04:00
indistinguishability obfuscation and learning problems
-
 1:24:58
1:24:58
indistinguishability obfuscation from simple-to-state hard problems
-
 1:04:00
1:04:00
tutorial on obfuscation
-
 56:30
56:30
indistinguishability obfuscation from well-founded assumptions
-
 1:14:51
1:14:51
the journey towards program obfuscation
-
 38:20
38:20
recent advances on foundations of program obfuscation
-
 22:36
22:36
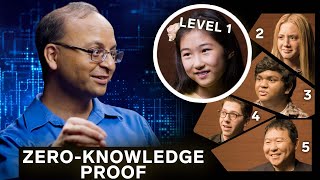
computer scientist explains one concept in 5 levels of difficulty | wired
-
 1:29:49
1:29:49
pairings in cryptography
-
 1:10:05
1:10:05
ddps | ‘regularized reduced order models for control of navier-stokes equations’
-
 43:40
43:40
obfuscation iii
-
 52:00
52:00
indistinguishability obfuscation via mathematical proofs of equivalence
-
 31:10
31:10
indistinguishability obfuscation, range avoidance, and bounded arithmetic
-
 1:05:51
1:05:51
on the assumptions used for obfuscation
-
 1:04:03
1:04:03
cryptanalysis of candidate program obfuscators
-
 53:54
53:54
attribute-based encryption for circuits
-
 53:11
53:11
lpn based io part 2
-
 56:40
56:40
tutorial: encrypted computation from lattices
-
 2:06
2:06
pushing the limits of minor allele frequency measurement - agbt 2015
-
 55:31
55:31
io via functional encryption: techniques and challenges from lwe