#pii #nist pt #privacy controls
Published 3 years ago • 484 plays • Length 0:59Download video MP4
Download video MP3
Similar videos
-
 0:59
0:59
#pii personally identifiable information and transparency #nist pt #privacy controls
-
 1:00
1:00
pii transparency nist 800 privacy controls pt-1, pt-2, pt-3
-
 0:59
0:59
nist 800 privacy and transparency controls pt-1
-
 0:59
0:59
cis 1.2 security controls map to nist 800 security controls #cybersecurity #informationsecurity #ni
-
 24:54
24:54
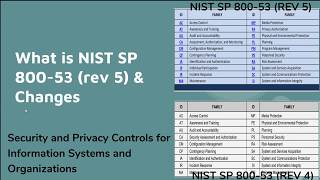
nist sp 800-53, revision 5 security controls for information systems and organizations - 1 overview
-
 2:35
2:35
nist notes - 'what's new in nist?' video series part 2: pii processing and transparency (pt)
-
 4:48
4:48
day-112: what is pii and phi? why is it important to protect?
-
 2:47
2:47
nist 800-171 control 3.13.9 - terminate network connections after a defined period of inactivity
-
 3:20
3:20
nist 800-171 control 3.13.10 - establish/manage cryptographic keys for cryptography employed in syst
-
 7:50
7:50
risk management framework nist 800-37 step 2: select security controls intro
-
 2:34
2:34
what guidance identifies federal information security controls for pii? - securityfirstcorp.com
-
 19:16
19:16
privacy on moderate impact systems (nist 800 rmf)
-
 3:56
3:56
privacy and personally identifiable information (pii)
-
 0:36
0:36
what is pii?
-
 1:00
1:00
learn what’s new in data privacy.
-
 2:22
2:22
nist 800-171 control 3.14.1: the key to timely system flaw correction
-
 2:45
2:45
nist 800-171 control 3.8.8 - prohibit the use of unidentifiable portable storage devices
-
 2:25
2:25
nist 800-171 control 3.1.22 -- control cui posted or processed on publicly accessible systems