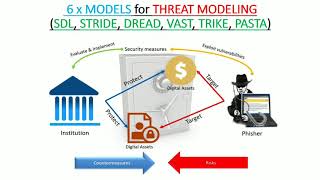
process for attack simulation & threat analysis (pasta)
Published 1 year ago • 648 plays • Length 5:54Download video MP4
Download video MP3
Similar videos
-
 0:59
0:59
how to use your custom threat library | process for attack simulation and threat analysis
-
 19:41
19:41
pasta threat modeling for cybersecurity | threat modeling example
-
 1:02:11
1:02:11
pasta threat modeling for cybersecurity | owasp all chapters 2020 presentation
-
 0:58
0:58
knowing the right data to use is key | process for attack simulation and threat analysis
-
 45:32
45:32
appsec eu 2017 threat modeling with pasta by tony ucedavelez
-
 21:49
21:49
stride threat modeling for beginners - in 20 minutes
-
 8:05
8:05
threat modeling frameworks for information security analysts | threats and attack vectors
-
 6:51
6:51
cybersecurity threat hunting explained
-
 36:30
36:30
what are the 7 stages of pasta threat modeling framework?
-
 0:55
0:55
know your complete attack surface with pasta threat modeling
-
 8:30
8:30
6 x threat modeling (sdl, stride, dread, vast, trike, pasta)
-
 20:03
20:03
pasta framework explained | threat hunting & modeling | tryhackme
-
 4:04
4:04
threat modeling - dread, pasta and stride methodologies
-
 4:52
4:52
pasta threat modeling | stage 1
-
 6:06
6:06
what is threat modeling and why is it important?
-
 7:21
7:21
simulate attacks with infection monkey | cyber security simulation, validation, and mitigation
-
 1:15:22
1:15:22
threat modeling explained| how to implement threat modeling| pros and cons of threat modeling method
-
 55:07
55:07
cyber attack simulator for security response training
-
 0:59
0:59
greater inclusion of security discipline with pasta threat modeling