public key cryptographic primitives in wireless sensor networks
Published 1 year ago • 18 plays • Length 18:07Download video MP4
Download video MP3
Similar videos
-
 1:27
1:27
a survey of public key cryptographic primitives in wireless sensor networks
-
 6:14
6:14
cryptographic key establishment in wireless sensor networks
-
 4:40
4:40
asymmetric encryption - simply explained
-
 9:44
9:44
public key cryptography
-
 22:32
22:32
watermarking public-key cryptographic primitives
-
 6:20
6:20
public key cryptography - computerphile
-
 15:46
15:46
how does public key cryptography work – gary explains
-
 13:34
13:34
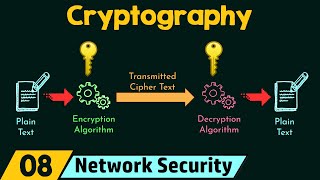
cryptography
-
 12:33
12:33
public and private keys - signatures & key exchanges - cryptography - practical tls
-
 6:57
6:57
key (cryptography)
-
 7:15
7:15
a secure data aggregation scheme based on appropriate cryptographic primitives in heterogeneous wsn
-
 11:31
11:31
combining cryptographic primitives to prevent jamming attacks in wireless networks new
-
 4:32
4:32
public key cryptography: what is it? | computer science | khan academy
-
 1:40
1:40
public key cryptography | chapter-4 | cryptography & network security | nesoacademy.org
-
 58:37
58:37
s-7: cryptographic primitives i
-
 20:38
20:38
lecture 20: security challenges in wsn part 1
-
 11:18
11:18
symmetric key cryptography vs asymmetric key cryptography | private vs public key cryptography