public key encryption with flexible pattern matching
Published 2 years ago • 181 plays • Length 20:49Download video MP4
Download video MP3
Similar videos
-
 4:40
4:40
asymmetric encryption - simply explained
-
 20:46
20:46
privacy-preserving pattern matching on encrypted data
-
 5:06
5:06
public key encryption (asymmetric key encryption)
-
 6:45
6:45
symmetric key and public key encryption
-
 1:24
1:24
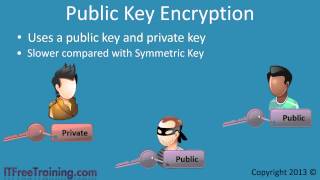
public key encryption
-
 3:35
3:35
public key, private message
-
 2:36
2:36
what is a passkey - and is it the future of online security? | bbc news
-
 5:11
5:11
private key vs. public key encryption explained | mark sanders
-
 4:22
4:22
formal verification of saber’s public-key encryption scheme in easycrypt
-
 21:38
21:38
multi-designated receiver signed public key encryption
-
 6:20
6:20
public key cryptography - computerphile
-
 3:10
3:10
it security tutorial - what is public key encryption?
-
 12:33
12:33
public and private keys - signatures & key exchanges - cryptography - practical tls
-
 20:16
20:16
simulation-based bi-selective opening security for public key encryption
-
 9:22
9:22
tech talk: what is public key infrastructure (pki)?
-
 0:47
0:47
public and private keys - georgia tech - health informatics in the cloud
-
 28:08
28:08
pattern matching on encrypted data -- paper review
-
 2:49
2:49
how encryption works - and how it can be bypassed
-
 1:49
1:49
other public key algorithms