rootkits (part 7): signature-based defense
Published 11 years ago • 1.3K plays • Length 6:00Download video MP4
Download video MP3
Similar videos
-
 7:06
7:06
rootkits (part 8): defense via hook detection
-
 6:03
6:03
rootkits (part 6): defense via cross-view detection
-
 13:36
13:36
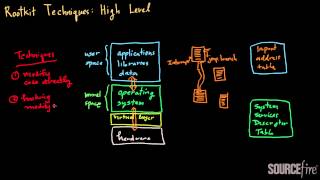
rootkits (part 2): high-level techniques
-
 5:37
5:37
rootkits as fast as possible
-
 2:15
2:15
how to fix safetynet on any rooted android phone
-
 8:18
8:18
how to detect rootkits on a computer or laptop by britec
-
 10:19
10:19
how to know if your pc is hacked? suspicious network activity 101
-
 2:45
2:45
rootkits - sy0-601 comptia security : 1.2
-
 8:18
8:18
rootkits (part 1): introduction and overview
-
 11:04
11:04
rootkits (part 3): direct kernel object manipulation
-
 6:05
6:05
ips detections: anomaly-based
-
 2:15
2:15
rootkit vs. bootkit - what is the difference between a rootkit and bootkit?
-
 0:51
0:51
what is a rootkit?
-
 7:02
7:02
malware protection techniques (part 1): overview
-
 6:12
6:12
trojans, rootkits and backdoors - security sy0-601 domain 1.2.4