rsa blind signatures solution - applied cryptography
Published 12 years ago • 3.2K plays • Length 1:01Download video MP4
Download video MP3
Similar videos
-
 1:37
1:37
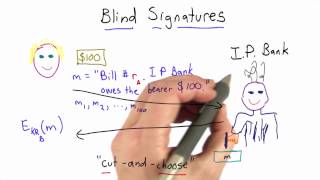
rsa blind signatures - applied cryptography
-
 1:31
1:31
blind signatures protocol solution - applied cryptography
-
 0:32
0:32
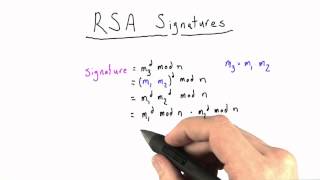
rsa signature solution - applied cryptography
-
 0:53
0:53
blind signatures protocol - applied cryptography
-
 2:24
2:24
blindfolded signatures - applied cryptography
-
 19:40
19:40
how does rsa cryptography work?
-
 16:31
16:31
public key cryptography: rsa encryption algorithm
-
 33:00
33:00
network security - digital signature algorithm (dsa)
-
 0:53
0:53
signatures solution - applied cryptography
-
 0:32
0:32
rsa signature - applied cryptography
-
 1:28
1:28
signatures - applied cryptography
-
 0:32
0:32
rsa encryption solution - applied cryptography
-
 1:13
1:13
back to signatures - applied cryptography
-
 0:16
0:16
rsa - applied cryptography
-
 0:46
0:46
security of rsa solution - applied cryptography
-
 9:13
9:13
rsa and blind signatures example
-
 0:26
0:26
worry solution - applied cryptography
-
 2:33
2:33
correctness and security solution - applied cryptography
-
 1:13
1:13
invertibility of rsa solution - applied cryptography
-
 1:17
1:17
correctness of rsa solution - applied cryptography
-
 0:23
0:23
correctness of rsa - applied cryptography