rsa cryptosystem - applied cryptography
Published 12 years ago • 3.3K plays • Length 2:36Download video MP4
Download video MP3
Similar videos
-
 0:24
0:24
rsa encryption - applied cryptography
-
 0:16
0:16
rsa - applied cryptography
-
 0:32
0:32
rsa encryption solution - applied cryptography
-
 0:23
0:23
correctness of rsa - applied cryptography
-
 19:40
19:40
how does rsa cryptography work?
-
 6:24
6:24
introduction to cryptography: rsa cryptosystem
-
 16:31
16:31
public key cryptography: rsa encryption algorithm
-
 8:40
8:40
the rsa encryption algorithm (1 of 2: computing an example)
-
 1:58
1:58
question 1 - applied cryptography
-
 0:55
0:55
invertibility of rsa - applied cryptography
-
 0:46
0:46
security of rsa solution - applied cryptography
-
 0:32
0:32
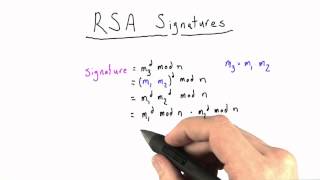
rsa signature - applied cryptography
-
 0:24
0:24
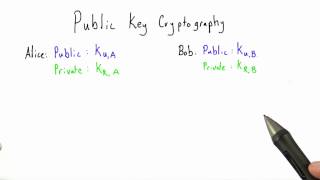
public key cryptography - applied cryptography
-
 2:20
2:20
asymmetric cryptosystems - applied cryptography
-
 2:16
2:16
security of rsa - applied cryptography
-
 1:59
1:59
summary - applied cryptography
-
 0:41
0:41
public key cryptography solution - applied cryptography
-
 0:48
0:48
insecurity in practice - applied cryptography
-
 0:32
0:32
rsa signature solution - applied cryptography
-
 2:44
2:44
do not implement your own crypto - applied cryptography