s-150: secret sharing
Published Streamed 3 years ago • 192 plays • Length 29:18Download video MP4
Download video MP3
Similar videos
-
 17:11
17:11
s-22: secret sharing
-
 26:08
26:08
quadratic secret sharing and conditional disclosure of secrets
-
 22:14
22:14
secret-sharing schemes for general and uniform access structures
-
 22:05
22:05
traceable secret sharing and applications
-
 1:29:46
1:29:46
s-22: secret sharing and coding
-
 20:42
20:42
the rise of paillier: homomorphic secret sharing and public-key silent ot
-
 28:25
28:25
revisiting non-malleable secret sharing
-
 22:56
22:56
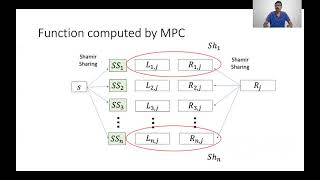
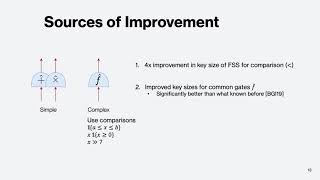
function secret sharing for mixed-mode and fixed-point secure computation
-
 4:28
4:28
(chinese) - personal hotspot setup srihome cctv internet online by using method (a) qr scan
-
 2:58
2:58
shamir’s secret sharing vs multisignature—which is best?
-
 5:19
5:19
how to apply sirim for imported smartphone in malaysia
-
 23:05
23:05
leakage-resilience of the shamir secret-sharing scheme against physical-bit leakages
-
 16:10
16:10
secret sharing using chinese remainder theory (crt)
-
 3:15
3:15
horcrux - shamir secret sharing in aleo
-
 0:31
0:31
6.08 lab 8 shamir's secret sharing scheme
-
 18:03
18:03
adaptive extractors and their application to leakage resilient secret sharing
-
 3:53
3:53
what is shamir’s secret sharing?
-
 4:47
4:47
shamir’s secret sharing (secure aggregation)
-
 1:19
1:19
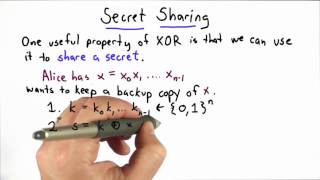
secret sharing - applied cryptography
-
 7:57
7:57
secret sharing explained visually
-
 23:01
23:01
nearly optimal robust secret sharing against rushing adversaries
-
 1:08
1:08
what is key sharding? shamir’s secret sharing explained