sans webcast: weaponizing browser based memory leak bugs
Published 6 years ago • 1.5K plays • Length 59:19Download video MP4
Download video MP3
Similar videos
-
 1:01:48
1:01:48
sans webcast: osint for pentesters finding targets and enumerating systems
-
 58:00
58:00
sans webcast: password cracking - beyond the basics
-
 1:00:59
1:00:59
sans webcast: practical osint - six tips for starting an effective investigation
-
 52:56
52:56
sans webcast: web application scanning automation
-
 24:07
24:07
sans webcast: enterprise discovery - i still haven’t found what i’m looking for
-
 1:04:37
1:04:37
sans webcast: osint for everyone - understanding risks and protecting your data
-
 1:04:07
1:04:07
sans pen test: webcast - if it fits, it sniffs adventures in warshipping
-
 53:59
53:59
sans webcast: security is qa - my path from developer to pen tester
-
 30:14
30:14
hunting and scoping a ransomware attack
-
 51:55
51:55
identifying library versions when remotely hacking linux vulnerabilities
-
 31:04
31:04
can you detect this? | inside the ransomware operator's toolkit
-
 49:03
49:03
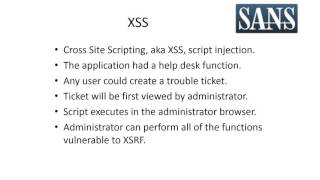
sans pen test webcast: complete application pwnage via multi post xsrf
-
 1:03:31
1:03:31
sans webcast: which sans pen test course should i take? w/ nmap demo
-
 1:02:42
1:02:42
sans webcast: sans pen test poster – blueprint: building a better pen tester
-
 55:26
55:26
sans webcast: passwords and authentication - get up to speed on attacks and defenses
-
 1:01:05
1:01:05
sans webcast: windows baselining and remote system assessment
-
 2:09
2:09
what makes for498: battlefield forensics & data acquisition such a great course?
-
 56:51
56:51
sans webcast: time is on your side username harvesting via timing attacks
-
 45:33
45:33
lookin’ for bugs in all the wrong places
-
 1:02:21
1:02:21
sans webcasts: how hackers run circles around our defenses (updated)
-
 0:42
0:42
what are the key takeaways of the sec542 class: web app penetration testing?
-
 1:02:36
1:02:36
sans webcast: so, you wanna be a pen tester 3 paths to consider