secure computation solution - applied cryptography
Published 9 years ago • 2.3K plays • Length 0:31Download video MP4
Download video MP3
Similar videos
-
 1:26
1:26
secure computation - applied cryptography
-
 1:07
1:07
secure shell solution - applied cryptography
-
 1:34
1:34
getting caught solution - applied cryptography
-
 3:12
3:12
signature validation solution - applied cryptography
-
 37:58
37:58
1. applied cryptography and trust: cryptography fundamentals (csn11131)
-
 5:06
5:06
how secure is 256 bit security?
-
 12:33
12:33
cryptography: crash course computer science #33
-
 1:15
1:15
encrypt outputs solution - applied cryptography
-
 2:53
2:53
file encryption solution - applied cryptography
-
 0:37
0:37
certificates and signatures solution - applied cryptography
-
 4:47
4:47
guessing keys solution - applied cryptography
-
 1:57
1:57
dh security - applied cryptography
-
 3:35
3:35
tls record protocol solution - applied cryptography
-
 2:33
2:33
proving security solution - applied cryptography
-
 0:32
0:32
rsa encryption solution - applied cryptography
-
 0:13
0:13
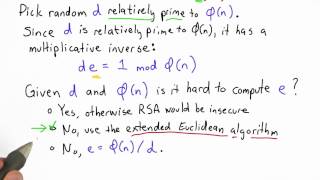
compute e solution - applied cryptography
-
 1:26
1:26
basic tls solution - applied cryptography
-
 2:33
2:33
correctness and security solution - applied cryptography
-
 0:41
0:41
compute d solution - applied cryptography
-
 0:36
0:36
wire labels - applied cryptography
-
 0:40
0:40
garbled circuit protocol solution - applied cryptography