secure hash algorithm explained (sha)
Published 6 years ago • 3.4K plays • Length 9:20Download video MP4
Download video MP3
Similar videos
-
 10:21
10:21
sha: secure hashing algorithm - computerphile
-
 2:14
2:14
secure hash algorithm
-
 14:50
14:50
sha 256 | sha 256 algorithm explanation | how sha 256 algorithm works | cryptography | simplilearn
-
 53:13
53:13
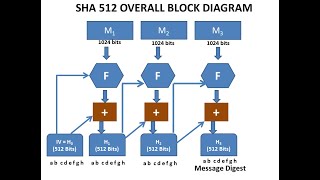
sha 512 - secure hash algorithm - step by step explanation - cryptography - cyber security - cse4003
-
 13:01
13:01
sha-256 | complete step-by-step explanation (w/ example)
-
 11:11
11:11
11 chapter 2 the sha 3 hash function
-
 9:09
9:09
sha 1 tutorial ,how sha 1 works, fips 180,secure hash algorithm tutorial
-
 17:04
17:04
instructions for solving the sha-265 cryptographic hash function
-
 26:58
26:58
sha-512 algorithm || secure hash algorithm || cryptographic hash functions || network security
-
 14:58
14:58
ins: unit-5 sha -512 (secure hash algorithm)
-
 9:45
9:45
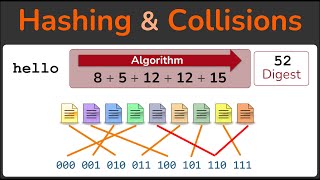
what is hashing? | what is hashing with example | hashing explained simply | simplilearn
-
 9:54
9:54
secure hash algorithm(sha-1) explained 2021 | sha working step by step | #cyberdefence #kluniversity
-
 22:42
22:42
sha-1 (secure hash algorithm) working in english | css series
-
 8:12
8:12
hashing algorithms and security - computerphile
-
 25:45
25:45
secure hash algorithm(sha1)
-
 12:16
12:16
how does sha-1 work - intro to cryptographic hash functions and sha-1
-
 11:42
11:42
hashing, hashing algorithms, and collisions - cryptography - practical tls
-
 32:04
32:04
secure hash algorithm (sha)
-
 10:52
10:52
sha-1 (secure hash algorithm - 1) part-1 working explained in hindi
-
 4:29
4:29
how hash function work?
-
 14:45
14:45
secure hash algorithm (sha-512) | information system security | cryptography | iss
-
 49:40
49:40
top hashing algorithms in cryptography | md5 and sha 256 algorithms explained | simplilearn