security analysis of spake2
Published 3 years ago • 1.3K plays • Length 26:43Download video MP4
Download video MP3
Similar videos
-
 16:09
16:09
security analysis of cpace
-
 1:17
1:17
security analysis of two password-authenticated multi-key exchange protocols
-
 16:55
16:55
security of the j-pake password-authenticated key exchange protocol
-
 10:14
10:14
how fido2 works and would it stop mfa fatigue attacks?
-
 2:36
2:36
what is a passkey - and is it the future of online security? | bbc news
-
 18:05
18:05
what is a passkey?
-
 21:47
21:47
how can passkeys possibly be safe?
-
 11:05
11:05
passwords vs. passkeys - fido bites back!
-
 9:36
9:36
pake - password authenticated key exchange
-
 15:51
15:51
verifpal cryptographic protocol analysis for students and engineers
-
 4:16
4:16
network authentication protocols at layer 2 (pap, chap & eap)
-
 6:55
6:55
wireless encryption - comptia a 220-1102 - 2.2
-
 1:27
1:27
security analysis of sasi protocol
-
 5:56
5:56
pap and chap - sy0-601 comptia security : 3.8
-
 26:36
26:36
ralf sasse, eth - security protocol verification techniques
-
 42:59
42:59
ccna security v2 - chapter 3 - authentication, authorization, and accounting
-
 8:20
8:20
final year projects | security analysis and implementation of 3-level security system using imag
-
 16:55
16:55
security of the j pake password authenticated key exchange protocol
-
 17:22
17:22
an extensive formal security analysis of the openid financial grade api pedram hosseyni
-
 8:56
8:56
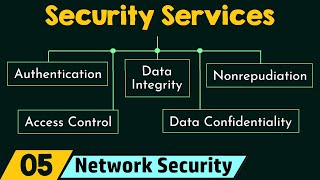
security services
-
 8:49
8:49
oauth 2.0 - pkce