sok: cryptographically protected database search
Published 7 years ago • 665 plays • Length 21:25Download video MP4
Download video MP3
Similar videos
-
 3:10
3:10
dorksearch
-
![find vulnerable services & hidden info using google dorks [tutorial]](https://i.ytimg.com/vi/u_gOnwWEXiA/mqdefault.jpg) 13:37
13:37
find vulnerable services & hidden info using google dorks [tutorial]
-
 11:50
11:50
protect your websites now! watch how hackers access database for usernames and passwords
-
 0:53
0:53
bitcanner bitcoin 💎 search space all private keys 💰 windows and android
-
 16:56
16:56
google hacking (use google search to hack!)
-
 17:09
17:09
nmap tutorial to find network vulnerabilities
-
 6:41
6:41
vulnerability scanning with nmap
-
 17:54
17:54
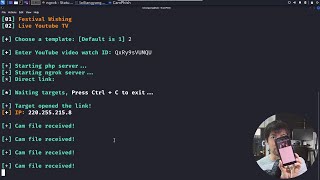
phishing attacks are scary easy to do!! (let me show you!) // free security // ep 2
-
 7:26
7:26
how hackers get any device location?! do not click this button on your browser!
-
 19:29
19:29
searching for system vulnerability exploits
-
 9:09
9:09
dehashed || a data breah search engine
-
 8:08
8:08
using shodan to search for vulnerable databases
-
 6:23
6:23
quantum hacking and how to protect yourself
-
![search for vulnerable devices around the world with shodan [tutorial]](https://i.ytimg.com/vi/oDkg1zz6xlw/mqdefault.jpg) 18:03
18:03
search for vulnerable devices around the world with shodan [tutorial]
-
 30:13
30:13
sok: tools for game theoretic models of security for cryptocurrencies - sarah azouvi
-
 1:13:52
1:13:52
investigating cerber ransomware with splunk | tryhackme boss of the soc v1
-
 33:12
33:12
queryable encryption - next-gen security for sensitive workloads
-
 8:03
8:03
how to find vulnerabilities and exploits
-
 6:09
6:09
do not click! else, your location will be exposed!
-
 5:27
5:27
searchsploit guide | finding exploits | kali linux