source 346 confidential 81 seemingly 83 linkage 166 republic 924 process
Published • 3 plays • Length 1:21Download video MP4
Download video MP3
Similar videos
-
 10:14
10:14
lec :03 cia triad | confidentiality, integrity and availability
-
 1:36
1:36
optimization of conveyor belt systems through advanced process control | continental
-
 0:13
0:13
industry responsibility
-
 6:48
6:48
enabling it modernization - secure, adaptive networks (episode 4, segment 4)
-
 8:00
8:00
role-based access control (rbac) explained: how it works and when to use it
-
 4:16
4:16
operations management: juggling tasks like a small biz ninja!
-
 3:18
3:18
革新的省配線ネットワーク anywireaslink - anywireaslink reduces wiring and offers an variety of added value.
-
 6:00
6:00
security operation center
-
 2:02
2:02
terminal 501 law 111 millennium 836 lien 884 incidentally 543 secrecy
-
 0:15
0:15
open enrollment
-
 3:47
3:47
automatically discover, classify, and lock down sensitive data
-
 18:45
18:45
materially adverse interests under rules 1.9 & 1.18 - aba formal op. 21-497
-
 4:04
4:04
transform your analog system: how acti encoders revolutionize security!
-
 0:41
0:41
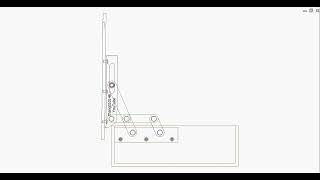
110 deg. concealed hinge of 6-bar linkage
-
 5:33
5:33
37 platform services private access order of operations
-
 0:46
0:46
24x7x365 security operations center
-
 1:20:15
1:20:15
approximate quantum error correcting code from conformal field theory
-
 7:29
7:29
kerberos constrained delegation
-
 18:42
18:42
ec'19: optimal auctions vs. anonymous pricing: beyond linear utility
-
 3:37
3:37
nist 800-171 control 3.12.2 – develop and implement plans of action
-
 37:50
37:50
exploring the social and ethical issues in data linkage, mandy chessell
-
 6:40
6:40
unlock operational excellence: dare to align with iso 14031!