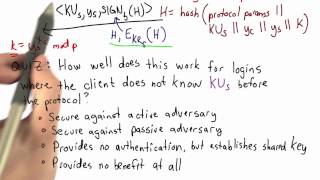
ssh authentication solution - applied cryptography
Published 12 years ago • 644 plays • Length 1:35Download video MP4
Download video MP3
Similar videos
-
 2:33
2:33
ssh authentication in practice - applied cryptography
-
 0:24
0:24
ssh authentication - applied cryptography
-
 1:07
1:07
secure shell solution - applied cryptography
-
 0:50
0:50
eke authentication solution - applied cryptography
-
 2:56
2:56
secure shell - applied cryptography
-
 5:58
5:58
how to use your pgp key for ssh authentication
-
 7:31
7:31
how ssh key works ?
-
 26:40
26:40
how to secure ssh | linux security with hackersploit
-
 0:44
0:44
wire labels solution - applied cryptography
-
 2:01
2:01
one time pad solution - applied cryptography
-
 0:23
0:23
useful certificates - applied cryptography
-
 0:26
0:26
eke authentication - applied cryptography
-
 0:32
0:32
cfb decryption solution - applied cryptography
-
 0:59
0:59
prove a vote solution - applied cryptography
-
 1:03
1:03
overview - applied cryptography
-
 1:12
1:12
eke authentication implementation solution - applied cryptography
-
 0:56
0:56
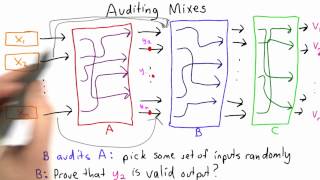
mixnet solution - applied cryptography
-
 1:17
1:17
trusting a server solution - applied cryptography
-
 0:13
0:13
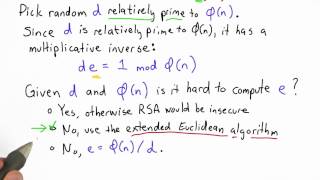
compute e solution - applied cryptography
-
 2:16
2:16
storing passwords solution - applied cryptography
-
 1:09
1:09
auditing mixes solution - applied cryptography