three must haves for any threat hunter
Published 3 years ago • 1.6K plays • Length 2:08Download video MP4
Download video MP3
Similar videos
-
 0:31
0:31
sentinelone activeedr - redefining threat hunting
-
 27:08
27:08
threat hunting with what you have
-
 6:51
6:51
cybersecurity threat hunting explained
-
 22:30
22:30
sentinelone training | part 5 - incidents
-
 8:17
8:17
what to do with a virus infection as a soc analyst | cybersecurity day in life
-
 8:54
8:54
what is xdr vs edr vs mdr? breaking down extended detection and response
-
 10:47
10:47
threat hunting tutorial: introduction
-
 1:24
1:24
application control with sentinelone
-
 3:14
3:14
basic incident test with eicar test file | part 1 | sentinelone
-
 1:01:52
1:01:52
introducing zeto: a utxo-based privacy-preserving tokens toolkit for evm
-
 3:18
3:18
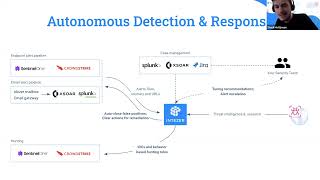
integrate intezer with sentinelone for automated alert triage and threat hunting
-
 40:38
40:38
advanced threat hunting with azure sentinel and sentinelone
-
 58:15
58:15
advanced incident response and threat hunting with sentinelone and intezer
-
 5:46
5:46
wannacry ransomware rollback with sentinelone tutorial | threat hunting and incident response
-
 53:36
53:36
technical workshop: milad aslaner | sentinelone
-
 17:10
17:10
security incident using huntress & sentinelone: what was found & what was missed 🚨
-
 32:31
32:31
modern threat hunting with your siem on a $0 budget - ryan fried - esw #284
-
 0:53
0:53
sentinelone vs dearcry ransomware (exploits microsoft hafnium exchange vulnerabilities) protect mode
-
 32:38
32:38
sentinelone has your cybersecurity evolved with the threats - webinar
-
 1:19
1:19
why sentinelone is perfect for your business security