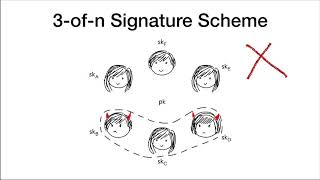
threshold ecdsa from ecdsa assumptions: the multiparty case
Published 5 years ago • 1.4K plays • Length 16:36Download video MP4
Download video MP3
Similar videos
-
 1:00
1:00
threshold ecdsa from ecdsa assumptions
-
 20:35
20:35
fast secure multiparty ecdsa
-
 5:07
5:07
ecdsa authentication explained using atecc108
-
 22:14
22:14
promise $\sigma$-protocol: how to construct efficient threshold ecdsa from encryptions based on...
-
 1:01
1:01
proactive threshold wallets with offline devices
-
 1:09:22
1:09:22
session on threshold signatures
-
 22:08
22:08
fast secure two party ecdsa signing
-
 7:49
7:49
how to get a public key from an ecdsa signature and its associated message
-
 7:09
7:09
performing deauthentication attack using aircrack-ng
-
 2:25
2:25
bypass latest 360加固 jiagu protection signature cheak
-
 46:43
46:43
threshold signatures and fault attacks
-
 27:49
27:49
on the security of ecdsa with additive key derivation and presignatures
-
 8:19
8:19
breaking ecdsa (elliptic curve cryptography) - rhme2 secure filesystem v1.92r1 (crypto 150)
-
 23:03
23:03
two-party ecdsa from hash proof systems and efficient instantiations
-
 23:16
23:16
threshold cryptosystems from threshold fully homomorphic encryption
-
 16:22
16:22
when one vulnerable primitive turns viral: novel single-trace attacks on ecdsa and rsa
-
 1:22:40
1:22:40
session on threshold cryptography
-
 27:12
27:12
threshold cryptography
-
 9:58
9:58
20 exploring ecdhe with ecdsa