top ibm i security vulnerabilities and how to address them
Published 3 years ago • 68 plays • Length 48:30Download video MP4
Download video MP3
Similar videos
-
 1:02:09
1:02:09
the pro’s guide to ibm i security fundamentals
-
 51:16
51:16
the pro's guide to ibm i security fundamentals
-
 58:37
58:37
beyond the basics object level security on ibm i (part 1)
-
 51:12
51:12
how to build the foundation of ibm i security defense
-
 1:04:29
1:04:29
virtual tape library (vtl) technology for ibm i
-
 4:21
4:21
noname advanced api security for ibm
-
 1:00:20
1:00:20
ibm i access client solutions for data access
-
 58:27
58:27
ibm i security for programmers
-
 51:02
51:02
how to avoid the biggest mistakes in ibm i security
-
 51:02
51:02
the biggest mistakes in ibm i security
-
 59:24
59:24
expert tips for ibm i security: beyond the basics
-
 57:49
57:49
5 ibm i security quick wins
-
 1:00:18
1:00:18
everything you need to know about ibm i 7.4
-
 50:55
50:55
ibm i security trends and threats to watch in 2022
-
 53:32
53:32
why your ibm i security will fail (and how to fix it)
-
 8:29
8:29
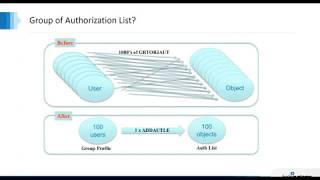
ibm i security - misconceptions - the authorization list
-
 46:42
46:42
cut through ibm i security confusion
-
 58:55
58:55
ibm i security for programmers part 2
-
 44:48
44:48
put ibm i security on the offense with pen testing
-
 1:05:01
1:05:01
the state of ibm i security in 2021: new data and simple ways to take action
-
 44:33
44:33
how to prevent and uncover suspicious activity on ibm i