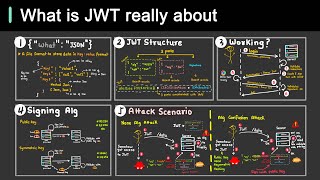
understanding jwt vulnerabilities: the 'none' vulnerability
Published 11 months ago • 117K plays • Length 19:25Download video MP4
Download video MP3
Similar videos
-
 5:02
5:02
understanding jwt vulnerabilities: jwt crack attack
-
 5:55
5:55
pentesting jwts: cracking weak keys using jwt_tool
-
 5:14
5:14
why is jwt popular?
-
 39:22
39:22
intro to jwt vulnerabilities
-
 16:33
16:33
introduction to jwt attacks
-
 6:30
6:30
json web token hacking
-
 12:23
12:23
jwt signature and validation explained
-
 9:29
9:29
jwts are insecure session tokens
-
 11:24
11:24
json web tokens (jwts) explained with examples | system design
-
 0:57
0:57
day 27: json web tokens (jwt) | #cybersecurityawarenessmonth 2023
-
 0:32
0:32
authentication and authorization using jwt token and roles-based access control
-
 1:07
1:07
how does jwt work
-
 7:39
7:39
attacking jwt for beginners!
-
 0:28
0:28
authentication vs authorization #shorts
-
 14:53
14:53
what is jwt and why should you use jwt