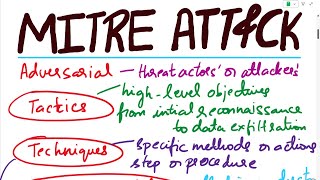
understanding the cyber kill chain and mitre att&ck | @sh3ll_5h0ck
Published 11 months ago • 102 plays • Length 6:35Download video MP4
Download video MP3
Similar videos
-
 13:18
13:18
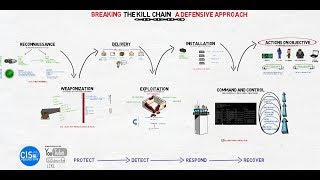
breaking the kill chain: a defensive approach
-
 26:15
26:15
taking security strategy to the next level: the cyber kill chain vs. mitre att&ck
-
 2:05
2:05
cyber kill chain: what it is, how it works
-
 6:44
6:44
the cyber kill chain
-
 5:52
5:52
mitre att&ck framework vs cyber kill-chain | how to use | what is it | rajneesh gupta
-
 3:43
3:43
mitre att&ck® framework
-
 42:16
42:16
putting mitre att&ck™ into action with what you have, where you are presented by katie nickels
-
 6:27
6:27
use mitre att&ck for threat hunting in cyber security | beginner
-
 8:57
8:57
the mitre att&ck framework for pentesters and ethical hackers
-
 7:53
7:53
mitre att&ck framework for beginners
-
 8:56
8:56
what is mitre att&ck | how can use mitre att&ck framework | cyber kill-chain | rajneesh gupta
-
 7:46
7:46
the anatomy of an att&ck
-
 2:40
2:40
the cyber kill chain explained with real examples (2024)
-
 13:55
13:55
the cyber kill chain and how to identify indicators of compromise
-
 5:11
5:11
attack frameworks: mitre att&ck/diamond model/cyber kill chain
-
 28:42
28:42
the cyber kill chain explained | threat intelligence | tryhackme
-
 7:31
7:31
what is cyber kill chain # the 7 steps of a cyberattack
-
 16:43
16:43
mitre attack | mitre att&ck | mitre att&ck explained with an example | mitre att&ck analysis
-
 47:58
47:58
how to apply the cyber kill chain framework to identify and combat cyberattacks
-
 4:42
4:42
learn the basics of the cyber kill chain
-
 2:41
2:41
mitre att&ck explained with phishing email | cyberres sme submission