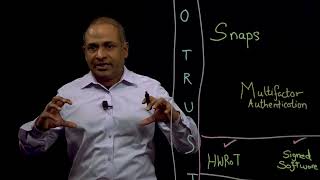
unlocking the power of zero trust in cybersecurity
Published 2 months ago • 35 plays • Length 0:55Download video MP4
Download video MP3
Similar videos
-
 22:26
22:26
unlocking the potential of zero trust in privileged access management
-
 1:01:02
1:01:02
unlock the real power of zero trust
-
 9:58
9:58
accelerate zero trust cybersecurity adoption with powerstore
-
 41:45
41:45
the fundamentals of zero trust for developers: how to automate and evolve your security operations
-
 9:42
9:42
12 home security gadgets that are next level
-
 4:39
4:39
zero trust in 5 minutes with brian deitch
-
 43:35
43:35
new zero trust innovations power cisco secure access
-
 46:08
46:08
i’ve got zero trust in my understanding of zero trust
-
 23:57
23:57
what is zero trust security? i nozomi networks
-
 25:58
25:58
5g and zero trust for maximum security
-
 13:46
13:46
breaking the kill chain: how zscaler disrupts attacks with zero trust network access
-
 1:21
1:21
alex simons explains how zscaler and microsoft together can achieve zero trust security model
-
 1:54
1:54
zero trust network access (ztna): enhancing cybersecurity in the digital age
-
 4:59
4:59
zero trust – your 3 step introduction guide.
-
 47:22
47:22
identity: the key to zero trust security
-
 2:56
2:56
mission possible: achieving zero trust security is now a reality
-
 33:51
33:51
implementing zero trust across the dod and beyond
-
 11:57
11:57
the zscaler tech sessions: seven elements of zero trust - control
-
 10:37
10:37
what is zero trust? | applying it in the real world
-
 28:15
28:15
where's the trust in zero trust?
-
 12:17
12:17
the zscaler tech sessions: seven elements of zero trust - verify
-
 11:14
11:14
unlock hidden power: simple steps to transform your life