usenix atc '21 - tcp-fuzz: detecting memory and semantic bugs in tcp stacks with fuzzing
Published 2 years ago • 689 plays • Length 13:10Download video MP4
Download video MP3
Similar videos
-
 10:32
10:32
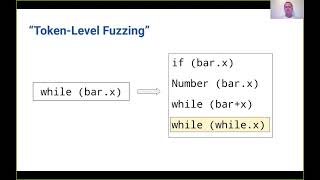
usenix security '21 - token-level fuzzing
-
 21:15
21:15
usenix atc '20 - fuzzan: efficient sanitizer metadata design for fuzzing
-
 20:31
20:31
usenix security '19 - detecting missing-check bugs via semantic- and context-aware
-
 12:09
12:09
usenix security '21 - preventing use-after-free attacks with fast forward allocation
-
 10:37
10:37
usenix security '20 - fuzzing error handling code using context-sensitive software fault injection
-
 11:58
11:58
usenix security '20 - greyone: data flow sensitive fuzzing
-
 11:43
11:43
usenix security '21 - syzvegas: beating kernel fuzzing odds with reinforcement learning
-
 4:46
4:46
how do i use the trig modifiers for fun effects on the elektron syntakt?
-
 10:35
10:35
tool setup and offset in linuxcnc
-
 3:07
3:07
nordson asymtek: fids-on-the-fly for dispensing applications with fiducials
-
 12:05
12:05
usenix security '21 - automatic firmware emulation through invalidity-guided knowledge inference
-
 11:14
11:14
usenix security '23 - polyfuzz: holistic greybox fuzzing of multi-language systems
-
 11:35
11:35
usenix security '21 - detecting kernel refcount bugs with two-dimensional consistency checking
-
 11:54
11:54
usenix security '20 - fuzzgen: automatic fuzzer generation
-
 10:10
10:10
usenix security '21 - arcus: symbolic root cause analysis of exploits in production systems
-
 12:28
12:28
usenix security '22 - thehuzz: instruction fuzzing of processors using golden-reference models for
-
 12:00
12:00
usenix security '21 - constraint-guided directed greybox fuzzing
-
 14:00
14:00
usenix atc '21 - riff: reduced instruction footprint for coverage-guided fuzzing
-
 13:10
13:10
usenix security '21 - breaking through binaries: compiler-quality instrumentation for better
-
 21:50
21:50
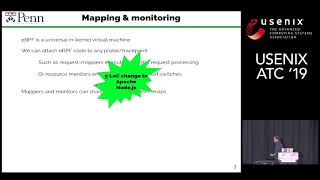
usenix atc '19 - detecting asymmetric application-layer denial-of-service attacks in-flight...