usenix security '16 - all your queries are belong to us: the power of file-injection attacks...
Published 2 years ago • 269 plays • Length 26:12Download video MP4
Download video MP3
Similar videos
-
 22:49
22:49
usenix security '16 - website-targeted false content injection by network operators
-
 31:09
31:09
usenix security '16 - unveil: a large-scale, automated approach to detecting ransomware
-
 27:59
27:59
usenix security '16 - thoth: comprehensive policy compliance in data retrieval systems
-
 10:18
10:18
usenix security '23 - qfa2sr: query-free adversarial transfer attacks to speaker recognition systems
-
 24:46
24:46
usenix security '16 - faster malicious 2-party secure computation with online/offline dual execution
-
 11:36
11:36
usenix security '23 - the impostor among us(b): off-path injection attacks on usb communications
-
 8:53
8:53
pc pro v7 lab 10 4 7
-
 2:34
2:34
how to check your protection against process injection for microsoft teams, zoom, webex
-
 8:27
8:27
injection attacks - types and how to prevent them
-
 12:03
12:03
usenix security '23 - know your cybercriminal: evaluating attacker preferences by measuring...
-
 14:53
14:53
usenix security '23 - csher: a system for compact storage with he-retrieval
-
 32:07
32:07
usenix security '16 - poking holes in information hiding
-
 27:11
27:11
usenix security '16 - predicting, decrypting, and abusing wpa2/802.11 group keys
-
 10:37
10:37
usenix security '20 - fuzzing error handling code using context-sensitive software fault injection
-
 10:05
10:05
usenix security '20 - poison over troubled forwarders: a cache poisoning attack targeting dns...
-
 13:15
13:15
usenix security '23 - pore: provably robust recommender systems against data poisoning attacks
-
 12:51
12:51
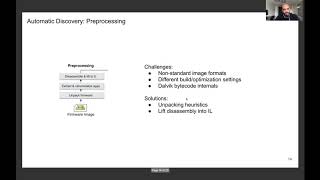
usenix security '20 - firmscope: automatic uncovering of privilege-escalation vulnerabilities
-
 26:04
26:04
usenix enigma 2016 - defending, detecting, and responding to hardware and firmware attacks