usenix security '20 - sys: a static/symbolic tool for finding good bugs in good (browser) code
Published 3 years ago • 1K plays • Length 11:57Download video MP4
Download video MP3
Similar videos
-
 11:08
11:08
usenix security '20 - symbolic execution with symcc: don't interpret, compile!
-
 10:37
10:37
usenix security '20 - fuzzing error handling code using context-sensitive software fault injection
-
 10:38
10:38
usenix security '20 - epic: every packet is checked in the data plane of a path-aware internet
-
 11:58
11:58
usenix security '21 - finding bugs using your own code: detecting functionally-similar yet
-
 10:32
10:32
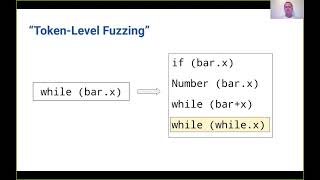
usenix security '21 - token-level fuzzing
-
 12:25
12:25
usenix security '23 - whip: improving static vulnerability detection in web application by...
-
 12:05
12:05
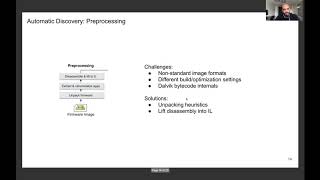
usenix security '21 - automatic firmware emulation through invalidity-guided knowledge inference
-
 13:38
13:38
usenix security '23 - detecting api post-handling bugs using code and description in patches
-
 12:14
12:14
usenix security '21 - understanding and detecting disordered error handling with precise function
-
 12:15
12:15
usenix security '20 - copycat: controlled instruction-level attacks on enclaves
-
 10:28
10:28
usenix security '20 - exploring connections between active learning and model extraction
-
 11:54
11:54
usenix security '20 - fuzzgen: automatic fuzzer generation
-
 10:41
10:41
usenix security '22 - fuzzorigin: detecting uxss vulnerabilities in browsers through origin fuzzing
-
 11:30
11:30
usenix security '22 - arbiter: bridging the static and dynamic divide in vulnerability discovery...
-
 20:31
20:31
usenix security '19 - detecting missing-check bugs via semantic- and context-aware
-
 12:51
12:51
usenix security '20 - firmscope: automatic uncovering of privilege-escalation vulnerabilities
-
 11:08
11:08
usenix security '23 - gleefuzz: fuzzing webgl through error message guided mutation
-
 12:05
12:05
usenix security '21 - undo workarounds for kernel bugs