usenix security '21 - identifying harmful media in end-to-end encrypted communication...
Published 2 years ago • 327 plays • Length 12:36Download video MP4
Download video MP3
Similar videos
-
 12:21
12:21
anunay kulshrestha - identifying harmful media in e2ee: efficient private membership computation
-
 12:13
12:13
usenix security '21 - express: lowering the cost of metadata-hiding communication with cryptographic
-
 12:12
12:12
usenix security '21 - evaluating in-workflow messages for improving mental models of end-to-end...
-
 12:16
12:16
usenix security '21 - searching encrypted data with size-locked indexes
-
 12:14
12:14
usenix security '21 - understanding and detecting disordered error handling with precise function
-
 12:30
12:30
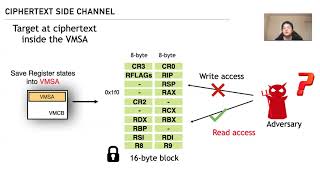
usenix security '21 - cipherleaks: breaking constant-time cryptography on amd sev via...
-
 32:40
32:40
nist framework and the nis2 eu cybersecurity directive - axonius
-
 11:48
11:48
usenix security '23 - xnids: explaining deep learning-based network intrusion detection systems...
-
 12:25
12:25
usenix security '22 - how to abuse and fix authenticated encryption without key commitment
-
 18:53
18:53
usenix security '22 - end-to-same-end encryption: modularly augmenting an app with an efficient
-
 11:21
11:21
usenix security '21 - definit: an analysis of exposed android init routines
-
 11:53
11:53
usenix security '21 - automated discovery of denial-of-service vulnerabilities in connected vehicle
-
 12:27
12:27
usenix security '21 - siamhan: ipv6 address correlation attacks on tls encrypted traffic
-
 11:56
11:56
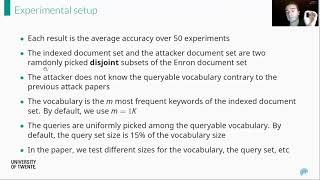
usenix security '21 - a highly accurate query-recovery attack against searchable encryption...
-
 11:27
11:27
usenix security '21 - v0finder: discovering the correct origin of publicly reported software
-
 12:18
12:18
usenix security '21 - share first, ask later (or never?) studying violations of gdpr's explicit
-
 11:12
11:12
usenix security '22 - frameshifter: security implications of http/2-to-http/1 conversion anomalies
-
 21:04
21:04
usenix security '19 - jedi: many-to-many end-to-end encryption and key delegation for iot