usenix security '21 - raccoon attack: finding and exploiting most-significant-bit-oracles...
Published 2 years ago • 461 plays • Length 11:38Download video MP4
Download video MP3
Similar videos
-
 39:11
39:11
raccoon attack: finding and exploiting most-significant-bit-oracles in tls-dh(e)
-
 12:13
12:13
usenix security '21 - alpaca: application layer protocol confusion - analyzing and mitigating cracks
-
 10:32
10:32
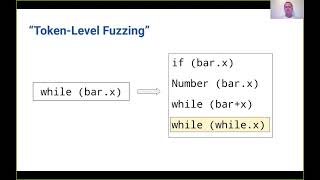
usenix security '21 - token-level fuzzing
-
 11:59
11:59
usenix security '21 - atlas: a sequence-based learning approach for attack investigation
-
 3:47
3:47
coyote pack surrounds and attacks raccoon warning may be upsetting to some .. twc san angelo, tx
-
 10:05
10:05
try not to laugh or smile | funny raccoon compilation 2017
-
 10:17
10:17
wireless attacks explained
-
 11:41
11:41
usenix security '20 - a formal analysis of ieee 802.11's wpa2: countering the kracks caused by...
-
 11:53
11:53
usenix security '21 - automated discovery of denial-of-service vulnerabilities in connected vehicle
-
 12:08
12:08
usenix security '21 - t-miner: a generative approach to defend against trojan attacks on dnn-based
-
 11:40
11:40
usenix security '21 - the role of computer security customer support in helping survivors...
-
 11:57
11:57
usenix security '21 - catching phishers by their bait: investigating the dutch phishing landscape
-
 12:01
12:01
usenix security '21 - the hijackers guide to the galaxy: off-path taking over internet resources
-
 9:31
9:31
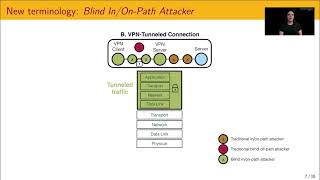
usenix security '21 - blind in/on-path attacks and applications to vpns
-
 11:56
11:56
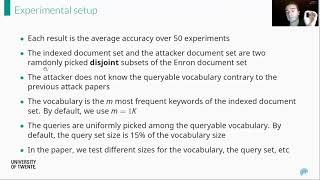
usenix security '21 - a highly accurate query-recovery attack against searchable encryption...
-
 12:06
12:06
usenix security '21 - lord of the ring(s): side channel attacks on the cpu on-chip ring...
-
 12:05
12:05
usenix security '21 - vscape: assessing and escaping virtual call protections
-
 11:44
11:44
usenix security '22 - loki: hardening code obfuscation against automated attacks
-
 12:35
12:35
usenix security '21 - assessing browser-level defense against idn-based phishing
-
 12:42
12:42
usenix security '21 - understanding malicious cross-library data harvesting on android
-
 21:11
21:11
usenix security '14 - man vs. machine: practical adversarial detection of malicious crowdsourcing