usenix security '22 - exploring the security boundary of data reconstruction via neuron exclusivity
Published 1 year ago • 215 plays • Length 12:24Download video MP4
Download video MP3
Similar videos
-
 12:59
12:59
usenix security '22 - poison forensics: traceback of data poisoning attacks in neural networks
-
 10:04
10:04
usenix security '22 - blacklight: scalable defense for neural networks against query-based black-box
-
 11:21
11:21
usenix security '22 - how and why people use virtual private networks
-
 11:49
11:49
usenix security '22 - security at the end of the tunnel: the anatomy of vpn mental models among
-
 11:12
11:12
usenix security '22 - frameshifter: security implications of http/2-to-http/1 conversion anomalies
-
 13:56
13:56
usenix security '22 - membership inference attacks and defenses in neural network pruning
-
 10:05
10:05
usenix security '22 - cheetah: lean and fast secure two-party deep neural network inference
-
 31:24
31:24
the security sandbox | evolving endpoint security in ot
-
 1:06:20
1:06:20
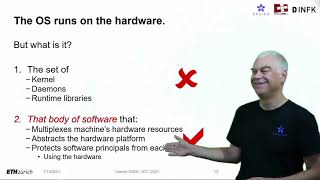
usenix atc '21/osdi '21 joint keynote address-it's time for operating systems to rediscover hardware
-
 11:27
11:27
cross-site scripting (xss) explained
-
 12:11
12:11
usenix security '22 - dos and don'ts of machine learning in computer security
-
 12:01
12:01
usenix security '21 - the hijackers guide to the galaxy: off-path taking over internet resources
-
 12:24
12:24
usenix security '22 - creating a secure underlay for the internet
-
 12:42
12:42
usenix security '21 - understanding malicious cross-library data harvesting on android
-
 13:04
13:04
usenix security '21 - where's crypto?: automated identification and classification of proprietary...
-
 12:12
12:12
usenix security '21 - graph backdoor
-
 10:28
10:28
usenix security '20 - exploring connections between active learning and model extraction