usenix security '22 - mining node.js vulnerabilities via object dependence graph and query
Published 1 year ago • 656 plays • Length 10:45Download video MP4
Download video MP3
Similar videos
-
 12:35
12:35
usenix security '23 - silent spring: prototype pollution leads to remote code execution in node.js
-
 11:45
11:45
usenix security '21 - abusing hidden properties to attack the node.js ecosystem
-
 12:52
12:52
usenix security '23 - trojan source: invisible vulnerabilities
-
 12:52
12:52
usenix security '23 - security analysis of mongodb queryable encryption
-
 12:37
12:37
usenix security '23 - your exploit is mine: instantly synthesizing counterattack smart contract
-
 14:56
14:56
install nessus for free and scan for vulnerabilities (new way)
-
 28:44
28:44
writing secure node code: avoiding the most common node.js security mistakes | basic security node.
-
 50:00
50:00
evaluating fuzz testing
-
 10:41
10:41
usenix security '22 - fuzzorigin: detecting uxss vulnerabilities in browsers through origin fuzzing
-
 12:51
12:51
usenix security '23 - nautilus: automated restful api vulnerability detection
-
 11:12
11:12
usenix security '22 - frameshifter: security implications of http/2-to-http/1 conversion anomalies
-
 12:00
12:00
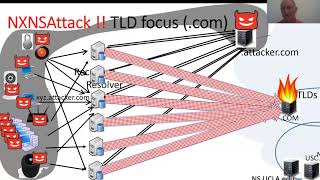
usenix security '20 - nxnsattack: recursive dns inefficiencies and vulnerabilities
-
 11:12
11:12
usenix security '23 - miner: a hybrid data-driven approach for rest api fuzzing
-
 13:16
13:16
usenix security '23 - a mixed-methods study of security practices of smart contract developers
-
 9:51
9:51
usenix security '23 - lost in conversion: exploit data structure conversion with attribute loss...