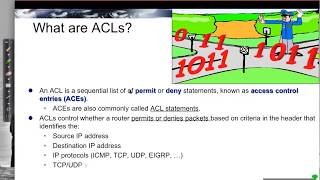
what are access lists? -- access control lists (acls) -- part 1 of 8
Published 3 years ago • 95K plays • Length 8:23Download video MP4
Download video MP3
Similar videos
-
 8:49
8:49
numbered acl syntax -- access control lists (acls) -- part 2 of 8
-
 18:42
18:42
understanding cybersecurity: access control lists (acls) part 1
-
 14:24
14:24
numbered acl configuration demonstration -- access control lists (acls) -- part 3 of 8
-
 14:02
14:02
access control lists (acl) part1
-
 10:12
10:12
acl placement: closer to the source or destination? -- access control lists (acls) -- part 8 of 8
-
 13:28
13:28
named acl configuration demonstration -- access control lists (acls) -- part 5 of 8
-
 8:46
8:46
10. wildcard masks acls
-
 12:46
12:46
how routing works: the basics, protocols, and real-world examples for beginners
-
 8:28
8:28
acl direction inbound vs outbound
-
 9:16
9:16
access lists part 1
-
 12:25
12:25
introduction to access control list (acl)
-
 5:30
5:30
introduction to access control lists
-
 5:00
5:00
named acl syntax -- access control lists (acls) -- part 4 of 8
-
 19:39
19:39
access control lists acls
-
 13:57
13:57
what is access control lists (acls)?
-
 26:14
26:14
9.1 ip acl operation (ccna 2: chapter 9: access control lists)
-
 11:34
11:34
ipv6 acls - syntax and demonstration -- access control lists (acls) -- part 6 of 8
-
 24:29
24:29
part 42. introduction of access control list (acl).
-
 18:48
18:48
ip access control lists (acls) | cisco ccna 200-301