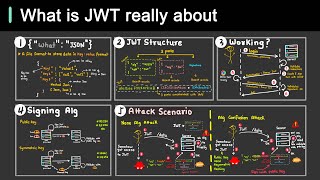
what are jwts and are they vulnerable to attacks? - api security with a pinch of salt
Published 4 years ago • 378 plays • Length 17:23Download video MP4
Download video MP3
Similar videos
-
 4:24
4:24
securing rest apis - jwt token explained in 4 minutes for beginners tutorial - s27e01
-
 5:14
5:14
why is jwt popular?
-
 4:50
4:50
jwt best practices for max security
-
 5:13
5:13
what is jwt ? json web token explained
-
 11:27
11:27
how does jwt authentication work? (json web token) | tokens vs sessions
-
 10:37
10:37
what is a jwt (json web token) and why your rest api needs it
-
 8:31
8:31
understanding json web tokens | jwt explanation from tech with tim
-
 7:00
7:00
session vs jwt: the differences you may not know!
-
 8:38
8:38
id tokens vs access tokens: what's the difference?
-
 37:18
37:18
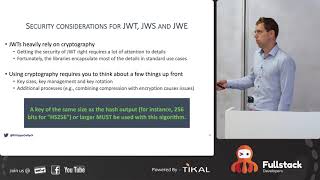
the parts of jwt security nobody talks about | philippe de ryck, google developer expert
-
 1:00
1:00
what is a jwt? 🆔⌛
-
 1:00
1:00
how jwt is used for authentication in microservices - short
-
 5:47
5:47
securing api testing: mastering jwt tokens for authentication in 2024
-
 14:53
14:53
what is jwt? json web tokens explained (java brains)
-
 20:36
20:36
#38 spring security | validating jwt token
-
 0:53
0:53
jwt token authentication - this is how it works
-
 9:18
9:18
jwt explained in under 10 minutes (json web tokens)
-
 0:27
0:27
what is jwt ? 🤔
-
 50:30
50:30
everything you wanted to know about working with and testing jwts and jwks by tony guimelli
-
 0:59
0:59
refactoring: decoding jwts with plain java #java #shorts
-
 10:25
10:25
jwt token vs server tokens
-
 0:57
0:57
decoding jwts with plain java #java #shorts