risk-based authorization with axiomatics and crowdstrike
Published 1 year ago • 337 plays • Length 2:18Download video MP4
Download video MP3
Similar videos
-
 4:33
4:33
what is risk-based authentication and what are its benefits?
-
 4:41
4:41
what is risk?
-
 3:40
3:40
risk based inspection ( rbi ) - pgas solution
-
 3:50
3:50
what is a risk register and when to use it
-
 13:37
13:37
risk-based authentication explained
-
 3:36
3:36
what is risk based security | centraleyes
-
 2:11
2:11
risk based authentication in action
-
 0:50
0:50
what's the future of rbac and abac? #axiominute #shorts
-
 3:09
3:09
what is risk-based inspection?
-
 1:59
1:59
batalas - what is risk-based thinking
-
 0:54
0:54
3 product trends in identity #axiominute #shorts
-
 2:12
2:12
security risk based authorization
-
 0:15
0:15
3 certification that make you better risk management professional #cybersecurity #crisc #grc
-
 58:29
58:29
webinar | fica: what is a risk-based approach?
-
 1:00
1:00
what air travel can teach us about zero trust #axiominute #shorts
-
 9:56
9:56
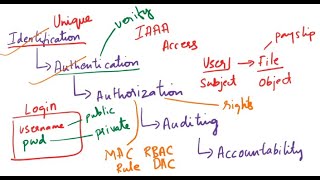
what is identification, authentication, authorization, auditing, accountability| iaaa| cybersecurity
-
 0:42
0:42
what is risk based testing? understand with the help of example #shorts #shortsvideo #tranding
-
 0:51
0:51
what is a pretrial #riskassessment? #shorts
-
 4:56
4:56
45 what is risk-based decision-making?
-
![what is risk-based thinking? [how to: iso 9001]](https://i.ytimg.com/vi/ZxgKfUsJpkc/mqdefault.jpg) 6:40
6:40
what is risk-based thinking? [how to: iso 9001]