where are threat actors discussing sap vulnerabilities?
Published 1 month ago • 54 plays • Length 0:51Download video MP4
Download video MP3
Similar videos
-
 0:59
0:59
how do threat actors price sap exploits?
-
 0:28
0:28
how are threat actors leveraging sap exploits?
-
 1:55
1:55
how are threat actors monetizing sap compromises?
-
 5:14
5:14
check windows 10 for serioussam and hivenightmare vulnerability
-
 23:17
23:17
your sap systems are under attack! learn how to detect and defend cyber attacks
-
 2:22
2:22
data-centric cybersecurity for sap: protecting against internal threats
-
 1:01
1:01
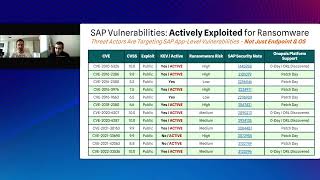
which sap vulnerabilities are being actively exploited by ransomware?
-
 4:56
4:56
then & now: onapsis co-founders discuss threats to sap & oracle applications
-
 1:22
1:22
are sap applications susceptible to ransomware?
-
 0:23
0:23
real-time sap threat monitoring: onapsis defend overview
-
 10:35
10:35
interview with greg kushmerek, onapsis
-
 1:02
1:02
protecting erp applications with onapsis
-
 0:29
0:29
the importance of patching vulnerabilities in cybersecurity | stay ahead of threat actors
-
 0:23
0:23
devsecops for sap: onapsis control overview
-
 15:52
15:52
frugé-ology episode 13: beers and a conversation on cyber threats targeting sap applications
-
 5:11
5:11
8/2/18 old oracle sap vulnerabilities still a threat | at&t threattraq
-
 25:16
25:16
episode 35: cyber threats to erp applications
-
 13:10
13:10
episode 9: the defenders digest
-
 50:35
50:35
cg - latest threats and vulnerabilities to mission-critical sap applications
-
 11:21
11:21
episode 10: the defenders digest