why policy-based access control is a superior solution for integrators and users alike
Published 2 years ago • 118 plays • Length 7:16
Download video MP4
Download video MP3
Similar videos
-
 1:06
1:06
what is pbac? policy based access control explainer by plainid
-
 8:00
8:00
role-based access control (rbac) explained: how it works and when to use it
-
 20:39
20:39
explain access control models| discretionary dac, mandatory mac, rbac, rule, attribute, risk based
-
 7:39
7:39
role-based access control (rbac) vs. attribute-based access control (abac)
-
 4:50
4:50
role based access control
-
 3:39
3:39
🔐 access control methods compared: rbac, abac, acl, and pbac - which one reigns supreme?
-
 2:17
2:17
how to create an access control policy
-
 10:04
10:04
access control - sy0-601 comptia security : 3.8
-
 29:16
29:16
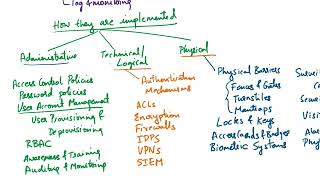
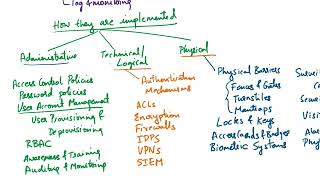
explain access control types| administrative, logical, physical| preventive, detective, compensating
-
 15:53
15:53
polisma - a framework for learning attribute-based access control policies
-
 14:02
14:02
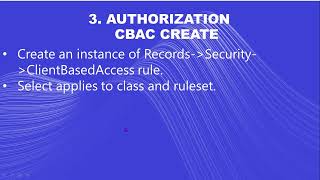
pega security through client based access control (cbac) and basic access control (bac) in pega 8
-
 22:14
22:14
abac 101 attribute based access control cissp csslp ccsp
-
 13:42
13:42
az-900 episode 28 | azure role-based access control (rbac)
-
 50:29
50:29
plainid masterclass: data access controls for business owners - june 25 | identiverse 2019
-
 0:59
0:59
why attribute-based access control is the only way to scale data usage securely.
-
 0:52
0:52
access control policies
-
 21:00
21:00
role based access control explained
-
 9:23
9:23
control center policy authoring tutorial- nextlabs policy-based access management
-
 3:20
3:20
what is attribute based access control (abac)?
Clip.africa.com - Privacy-policy
 1:06
1:06
 8:00
8:00
 20:39
20:39
 7:39
7:39
 4:50
4:50
 3:39
3:39
 2:17
2:17
 10:04
10:04
 29:16
29:16
 15:53
15:53
 14:02
14:02
 22:14
22:14
 13:42
13:42
 50:29
50:29
 0:59
0:59
 0:52
0:52
 21:00
21:00
 9:23
9:23
 3:20
3:20