wireless authentication and key generation
Published 10 years ago • 91K plays • Length 23:37Download video MP4
Download video MP3
Similar videos
-
 15:14
15:14
wireless security
-
 4:55
4:55
secure wifi: wpa auth & key exchange in 802.11 | computer networks ep 8.8.1 | kurose & ross
-
 14:40
14:40
25 802 1x and eap concepts
-
 18:05
18:05
understand how the dot1x (802.1x) protocol works
-
 12:23
12:23
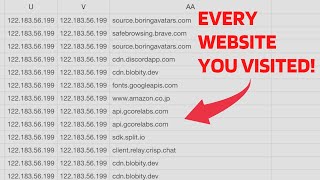
how hackers spy on you from your own wifi!
-
 13:12
13:12
port security vs port based authentication (802.1x) whats the difference?
-
 6:39
6:39
configure wireless client authentication in a centralized deployment
-
 0:15
0:15
growing up pentecostal... #short
-
 3:40
3:40
2 configure the cisco wlc for wireless client 802 1x authentication
-
 0:28
0:28
this can happen in thailand
-
 5:36
5:36
troubleshooting psk and 802.1x wireless authentication
-
 5:54
5:54
securing 5g: authentication & key exchange in cellular | computer networks ep. 8.8.2 | kurose & ross
-
 7:26
7:26
raspberry pi 802.11i enterprise security
-
 8:15
8:15
wireless authentication methods - sy0-601 comptia security : 3.4
-
 23:27
23:27
cyber threats, wireless security & digital hygiene: a conversation with dr. brett walkenhorst (pa...
-
 1:04:29
1:04:29
802.11i security analysis: can we build a secure wlan?
-
 16:36
16:36
ruckus wireless client association process - discovery, authentication, association and handshake
-
 12:53
12:53
802.1x authentication and 4-way handshake for wifi
-
 50:55
50:55
wireless - security (hd)
-
 24:38
24:38
ultimate s-tier wifi security with eap-tls certificates (feat. smallstep)