work from home: threats, vulnerabilities, and strategies for protecting your network
Published 3 years ago • 419 plays • Length 46:17Download video MP4
Download video MP3
Similar videos
-
 18:11
18:11
risks, threats, and vulnerabilities in moving to the cloud
-
 59:23
59:23
a cybersecurity engineering strategy for devsecops
-
 16:12
16:12
3 api security risks (and how to protect against them)
-
 36:45
36:45
security requirements engineering
-
 14:51
14:51
a technical strategy for cybersecurity
-
 51:05
51:05
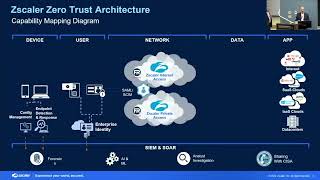
zscaler
-
 2:56
2:56
watch this russian hacker break into our computer in minutes | cnbc
-
 48:43
48:43
a model-based tool for designing safety-critical systems
-
 30:25
30:25
zero trust adoption: benefits, applications, and resources
-
 35:01
35:01
the cert guide to coordinated vulnerability disclosure
-
 38:29
38:29
best practices and lessons learned in standing up an aisirt
-
 15:41
15:41
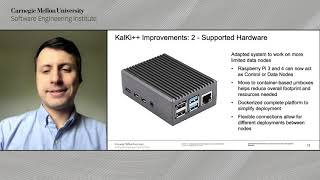
kalki : a scalable and extensible iot security platform
-
 58:55
58:55
ransomware: defense and resilience strategies
-
 49:44
49:44
using open source to shrink the cyber workforce gap
-
 1:55
1:55
r-eactr: a framework for designing realistic cyber warfare exercises
-
 1:01:23
1:01:23
threats for machine learning
-
 22:05
22:05
cybersecurity assurance leader
-
 31:02
31:02
a deep dive into dismantling disinformation - with luke osterritter
-
 1:02:06
1:02:06
what is cybersecurity engineering and why do i need it?
-
 31:13
31:13
software architecture patterns for robustness
-
 1:02:12
1:02:12
helping you reach the next level of security - 6 free tools for creating a cyber simulator