access control (its335, l08, y15)
Published 8 years ago • 2.3K plays • Length 1:04:25Download video MP4
Download video MP3
Similar videos
-
 39:27
39:27
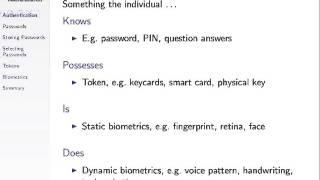
token and biometric authentication (its335, l08, y15)
-
 1:17:03
1:17:03
access control and linux permissions (its335, lecture 10, 2013)
-
 1:16:22
1:16:22
user authentication and passwords (its335, l06, y15)
-
 41:12
41:12
malicious software and countermeasures (its335, l11, y15)
-
 1:13:58
1:13:58
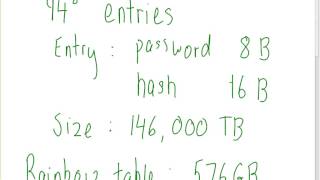
salted passwords and rainbow tables (its335, l07, y15)
-
 1:21:29
1:21:29
passwords, hashes and salt (its335, lecture 8, 2013)
-
 1:18:56
1:18:56
user authentication and passwords (its335, lecture 7, 2013)
-
 3:14
3:14
how to program the johnson controls system 450
-
 1:18:36
1:18:36
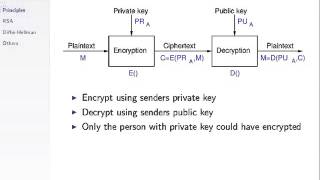
meet-in-the-middle attack (css441, l07, y15)
-
 13:53
13:53
surface cage technology & spinal fusion kevin yoo, md
-
 1:05:33
1:05:33
user authentication and passwords (its335, l7, y14)
-
 1:07:07
1:07:07
message authentication codes (css441, l16, y15)
-
 1:19:07
1:19:07
authentication with hash functions (its335, l05, y14)
-
 1:11:57
1:11:57
https (css441, l23, y15)
-
 1:03:24
1:03:24
secure shell (css441, l24, y15)
-
 17:15
17:15
basics of encryption (css441, l01, y15)
-
 8:58
8:58
key-based authentication in ssh (css441, l25, y15)
-
 1:04:50
1:04:50
public key cryptography (css441, l13, y15)