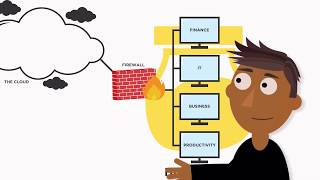
hacker highschool ▶︎ honeypots, honeynets and canary tokens
Published 2 years ago • 951 plays • Length 5:00Download video MP4
Download video MP3
Similar videos
-
 7:23
7:23
how to use canary tokens for threat hunting
-
 18:03
18:03
canarytokens - honeypots made easy
-
 12:36
12:36
how to setup canary tokens - home made honeypots 🍯
-
 0:52
0:52
what are honeytokens or canary tokens? quick explainer
-
 1:13
1:13
what is a honeypot?
-
 4:06
4:06
introducing canary tokens
-
 18:26
18:26
what is a honeypot? | how-to setup & install (walkthrough)
-
 2:35
2:35
what is a honeypot (cybersecurity)? honeypot benefits and risks
-
 7:10
7:10
how to avoid memecoin scams, rugpulls and honeypots (the easy way)
-
 8:33
8:33
honeypots in cyber security **explained**
-
 4:08
4:08
honeypots & honeynets
-
 4:48
4:48
ssh honeypot in 4 minutes - trap hackers in your server
-
 4:21
4:21
honeypot explained: complete setup & installation guide (easy walkthrough)
-
 9:40
9:40
easiest way to set up a honeypot!: ten minute tutorials
-
 0:46
0:46
what are honeytokens?
-
 0:39
0:39
honeypots in cybersecurity 🍯 trap the hackers!
-
 0:59
0:59
types of honeypots commonly used in cybersecurity
-
 2:18
2:18
honeypot | what is honeypot in simple words?
-
 21:42
21:42
build your own canarytoken server - canarytoken