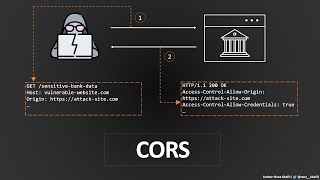
cors exploit
Published 2 years ago • 4.7K plays • Length 1:20Download video MP4
Download video MP3
Similar videos
-
 52:17
52:17
cross-origin resource sharing (cors) | complete guide
-
 5:41
5:41
cross origin resource sharing (cors) vulnerability | bugbountytraining | bug bounty service
-
 36:43
36:43
appsec eu 2017 exploiting cors misconfigurations for bitcoins and bounties by james kettle
-
 1:50
1:50
exploiting cors misconfiguration
-
 2:24
2:24
cors misconfiguration poc || bug bounty poc
-
 15:34
15:34
cors exploit ( the proper way ). 2 methods for cors detection and exploit for bug bounty hunters
-
 6:06
6:06
learn cors in 6 minutes
-
 9:31
9:31
hands-on guide to cors
-
 43:40
43:40
i found minecraft's most dangerous glitch
-
 15:01
15:01
poc for cross-origin resource sharing (cors) misconfiguration allowing unauthorized data access
-
 9:20
9:20
cross site request forgery - computerphile
-
 1:27
1:27
cors misconfiguration | leads to sensitive information | bug bounty poc
-
 11:05
11:05
ethical hacking in 100 seconds // and why do we need cors?
-
 2:51
2:51
cors || bypass cors misconfiguration leads to sensitive exposure poc || cashfree || bug bounty
-
 2:31
2:31
cors in 100 seconds
-
 17:19
17:19
covering the under rated vulnerabilities: cors misconfiguration #1
-
 9:39
9:39
what is cors vulnerability | cors misconfiguration explain
-
 45:37
45:37
james kettle - exploiting cors misconfigurations for bitcoins and bounties - appsecusa 2016
-
 5:54
5:54
cors exploit (xss console)
-
![how to solve cors error in 2 min [watch this] | cors explained in easy way](https://i.ytimg.com/vi/Odqih2oSmig/mqdefault.jpg) 2:57
2:57
how to solve cors error in 2 min [watch this] | cors explained in easy way
-
 9:31
9:31
cross-site scripting (xss) explained and demonstrated by a pro hacker!