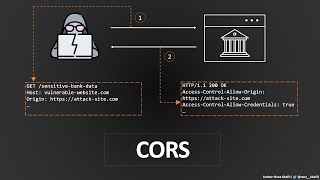
cross origin resource sharing (cors) vulnerability | bugbountytraining | bug bounty service
Published 1 year ago • 6.6K plays • Length 5:42Download video MP4
Download video MP3
Similar videos
-
 2:53
2:53
what are cross-origin resource sharing (cors) vulnerabilities | owasp top 10 | bug bounty service
-
 2:24
2:24
cors misconfiguration poc || bug bounty poc
-
 1:47
1:47
$$$ bounty | insecure cors misconfiguration with full exploitation | bug bounty poc |
-
 52:17
52:17
cross-origin resource sharing (cors) | complete guide
-
 3:34
3:34
cors ( cross-origin resource sharing) | exploitation | bug bounty poc
-
 8:15
8:15
что такое cors и зачем он нужен? по простому
-
 8:55
8:55
demystifying cors vulnerabilities: how attackers exploit cors to steal api keys
-
 8:46
8:46
2024 bug bounty recon basics
-
 1:01
1:01
how to fix cors vulnerability
-
 2:51
2:51
cors || bypass cors misconfiguration leads to sensitive exposure poc || cashfree || bug bounty
-
 2:32
2:32
what is cors cross-origin resource sharing || bug bounty || poc || 2022
-
 1:27
1:27
cross origin resource sharing (cors) || hacker || bug bounty
-
 3:11
3:11
cross-origin resource sharing (cors)
-
 2:18
2:18
🛑 cors misconfiguration
-
 1:50
1:50
exploiting cors misconfiguration
-
 4:26
4:26
corsscanner fast cors misconfiguration vulnerabilities scanner🍻
-
 15:34
15:34
cors exploit ( the proper way ). 2 methods for cors detection and exploit for bug bounty hunters
-
 0:59
0:59
bug bounty real target (cors) | cross-origin resource sharing: arbitrary origin trusted ( poc)
-
 2:31
2:31
cors in 100 seconds
-
 1:31
1:31
1-liner to identify cors misconfiguration