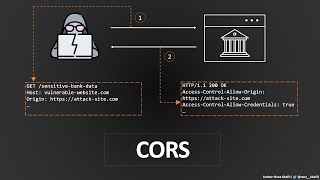
🛑 cors misconfiguration
Published 2 years ago • 688 plays • Length 2:18Download video MP4
Download video MP3
Similar videos
-
 5:41
5:41
cross origin resource sharing (cors) vulnerability | bugbountytraining | bug bounty service
-
 52:17
52:17
cross-origin resource sharing (cors) | complete guide
-
 9:39
9:39
what is cors vulnerability | cors misconfiguration explain
-
 1:50
1:50
exploiting cors misconfiguration
-
 42:56
42:56
#9 belajar cyber security - cross-origin resource sharing (cors)
-
 15:01
15:01
poc for cross-origin resource sharing (cors) misconfiguration allowing unauthorized data access
-
 8:23
8:23
corb - http203
-
 17:14
17:14
ep. 3 - same-origin policy
-
 1:04:43
1:04:43
same-origin policy: the core of web security @ owasp wellington
-
 17:32
17:32
#10 belajar cyber security - cross-origin resource sharing (cors)
-
 12:18
12:18
what is sop and cors? | cyber security | ethical hacking infosectrain
-
 0:23
0:23
cors (cross-origin resource sharing)
-
 16:02
16:02
security misconfigurations bwapp || cross origin resource sharing || cors || cyber world hindi
-
 36:43
36:43
appsec eu 2017 exploiting cors misconfigurations for bitcoins and bounties by james kettle
-
 1:37
1:37
exploiting cors misconfiguration using xss
-
 6:32
6:32
implementing cors security
-
 8:26
8:26
what is cors? | cross-origin resource sharing | cors explained!
-
 8:11
8:11
csrf and cors explained
-
 39:47
39:47
evan johnson - misconfigured cors and why web appsec is not getting easier - appsecusa 2016