cors vulnerability with internal network pivot attack
Published 3 years ago • 326 plays • Length 7:27Download video MP4
Download video MP3
Similar videos
-
 3:58
3:58
cors vulnerability with internal network pivot attack
-
 36:48
36:48
cors - lab #4 cors vulnerability with internal network pivot attack | long video
-
 4:34
4:34
cors vulnerability with internal network pivot attack-web security academy
-
 35:02
35:02
cors - lab #4 cors vulnerability with internal network pivot attack | short video
-
 5:58
5:58
cors vulnerability with internal network pivot attack (video solution) | 2020 -2021
-
 3:35
3:35
cors vulnerability with trusted null origin | web security academy lab
-
 3:54
3:54
cors vulnerability with trusted insecure protocols | web security academy lab
-
 2:20:08
2:20:08
web security academy | cors | 4 - internal network pivot attack
-
 15:34
15:34
cors exploit ( the proper way ). 2 methods for cors detection and exploit for bug bounty hunters
-
 48:11
48:11
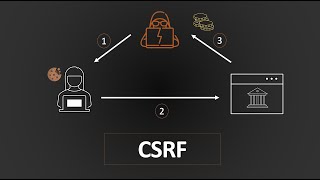
cross-site request forgery (csrf) | complete guide
-
 1:26:17
1:26:17
cobit 2019 executive overview - insights into the framework and implementation
-
 3:07
3:07
cors vulnerability with basic origin reflection | web security academy lab
-
 5:41
5:41
cross origin resource sharing (cors) vulnerability | bugbountytraining | bug bounty service
-
 16:41
16:41
cors - lab #1 cors vulnerability with basic origin reflection | long video
-
 14:24
14:24
résolution de cors vulnerability with internal network pivot attack avec owasp zap.
-
 52:17
52:17
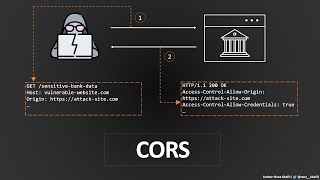
cross-origin resource sharing (cors) | complete guide
-
 20:21
20:21
cors - lab #3 cors vulnerability with trusted insecure protocols | short video
-
 1:06:03
1:06:03
module 11 hacking wireless network
-
 2:31
2:31
cors in 100 seconds
-
 12:10
12:10
cors - lab #1 cors vulnerability with basic origin reflection | short video
-
 2:16
2:16
cobit 2019 explained in two minutes - ben kalland
-
 7:05
7:05
lab cors vulnerability with trusted insecure protocols