data access explained: rbac, abac & jit
Published 1 year ago • 126 plays • Length 41:55Download video MP4
Download video MP3
Similar videos
-
 7:39
7:39
role-based access control (rbac) vs. attribute-based access control (abac)
-
 8:00
8:00
role-based access control (rbac) explained: how it works and when to use it
-
 3:03
3:03
rbac vs abac | identity & access management | iam
-
 20:28
20:28
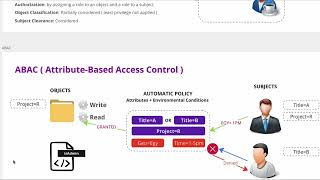
understanding attribute based access control (abac)
-
 1:29
1:29
why abac instead of rbac?
-
 3:42
3:42
attribute based access control
-
 4:53
4:53
rbac vs abac vs xbac for data access control
-
 1:58
1:58
elon musk fires employees in twitter meeting dub
-
 18:36
18:36
rbac & abac: гибридное решение для управления правами доступа
-
 13:42
13:42
az-900 episode 28 | azure role-based access control (rbac)
-
 13:45
13:45
authorization 101 for developers | rbac, rebac, and abac
-
 20:39
20:39
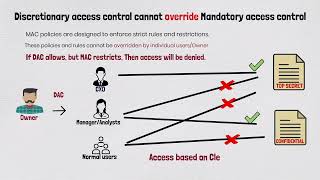
explain access control models| discretionary dac, mandatory mac, rbac, rule, attribute, risk based
-
 3:39
3:39
🔐 access control methods compared: rbac, abac, acl, and pbac - which one reigns supreme?
-
 10:33
10:33
abac and rbac in azure
-
 11:55
11:55
fundamentals of rbac and abac|how role based access control works|what is abac| best practices
-
 11:47
11:47
cyber security access models ( dac, mac, rbac and abac ) - arabic
-
 20:39
20:39
cyber security day 14 data access controls dac mac rbac abac comptia security
-
 3:07
3:07
access control models: why discretionary access control cannot override mandatory access control?
-
 0:58
0:58
🔐 video short: postgresql rbac vs abac - choosing the right access control model
-
 1:51
1:51
an overview of aws iam use cases: rbac, abac, and list permissions
-
 58:15
58:15
authorization modeling: design your rbac, abac, rebac