data integrity and hash function
Published 1 year ago • 1.4K plays • Length 7:17Download video MP4
Download video MP3
Similar videos
-
 9:45
9:45
what is hashing? | what is hashing with example | hashing explained simply | simplilearn
-
 2:36
2:36
what is hashing? hash functions explained simply
-
 8:43
8:43
hashed message authentication code hmac
-
 13:56
13:56
hash tables and hash functions
-
 2:10
2:10
module 5: what is hashing?
-
 8:12
8:12
hashing algorithms and security - computerphile
-
 4:29
4:29
how hash function work?
-
 7:28
7:28
passwords & hash functions (simply explained)
-
 15:24
15:24
cryptographic hash functions: part 1
-
 5:43
5:43
what are cryptographic hash functions?
-
 8:05
8:05
hash functions
-
 7:08
7:08
what is a cryptographic hashing function? (example purpose)
-
 16:47
16:47
cryptography: message integrity
-
 4:48
4:48
what is hashing on the blockchain?
-
 3:14
3:14
hash function - cs101 - udacity
-
 4:27
4:27
5 key principles - confidentiality, integrity, availability, authentication, nonrepudiation inform
-
 22:39
22:39
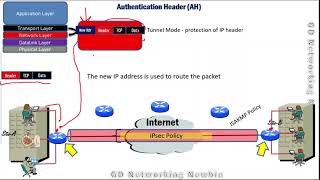
authentication header (ah) and encapsulating security payload (esp)
-
 11:16
11:16
hashes 4 hash functions for strings
-
 3:48
3:48
double hash - applied cryptography
-
 1:22:01
1:22:01
21. cryptography: hash functions
-
 6:49
6:49
what is a hash function?