double hash - applied cryptography
Published 12 years ago • 5.4K plays • Length 3:48Download video MP4
Download video MP3
Similar videos
-
 0:36
0:36
double hash solution - applied cryptography
-
 3:28
3:28
cryptographic hash function - applied cryptography
-
 1:56
1:56
salted password scheme - applied cryptography
-
 1:26
1:26
hash chain - applied cryptography
-
 0:47
0:47
hashing and eke - applied cryptography
-
 0:21
0:21
deanonymizing double spenders solution - applied cryptography
-
 1:15
1:15
one way function - applied cryptography
-
 0:57
0:57
padding - applied cryptography
-
 48:05
48:05
applied cryptography and trust: 3. hashing
-
 0:50
0:50
hash collision - applied cryptography
-
 2:23
2:23
cryptographic hash function solution - applied cryptography
-
 1:34
1:34
hash collision solution - applied cryptography
-
 0:52
0:52
proofs of work - applied cryptography
-
 2:31
2:31
provide scarcity - applied cryptography
-
 0:54
0:54
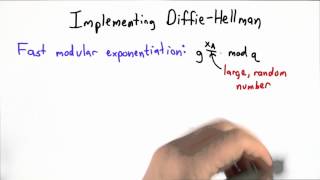
implementing dh - applied cryptography
-
 1:59
1:59
hash chain solution - applied cryptography
-
 59:57
59:57
3. applied cryptography and trust: hashing methods (csn11131)