eke authentication implementation - applied cryptography
Published 12 years ago • 1.7K plays • Length 1:11Download video MP4
Download video MP3
Similar videos
-
 1:12
1:12
eke authentication implementation solution - applied cryptography
-
 0:26
0:26
eke authentication - applied cryptography
-
 0:50
0:50
eke authentication solution - applied cryptography
-
 0:47
0:47
hashing and eke - applied cryptography
-
 0:30
0:30
hashing and eke solution - applied cryptography
-
 22:08
22:08
fast secure two party ecdsa signing
-
 8:12
8:12
avispa-eke protocol tutorial
-
 46:51
46:51
threshold cryptography 1 (crypto 2023)
-
 0:48
0:48
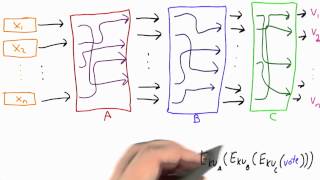
mixnet - applied cryptography
-
 5:53
5:53
demo - applied cryptography
-
 0:54
0:54
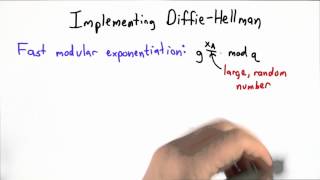
implementing dh - applied cryptography
-
 2:33
2:33
ssh authentication in practice - applied cryptography
-
 0:54
0:54
cbc implementation - applied cryptography
-
 1:35
1:35
welcome - applied cryptography
-
 0:24
0:24
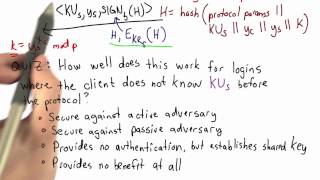
ssh authentication - applied cryptography
-
 1:42
1:42
key exchange - applied cryptography
-
 2:55
2:55
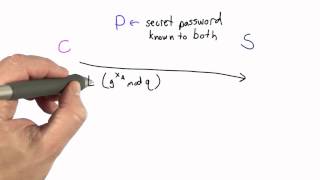
encrypted key exchange - applied cryptography
-
 1:00
1:00
summary - applied cryptography
-
 1:30
1:30
encrypted key exchange solution - applied cryptography
-
 33:13
33:13
applied cryptography
-
 0:37
0:37
certificates and signatures solution - applied cryptography