hashing and eke solution - applied cryptography
Published 9 years ago • 262 plays • Length 0:30Download video MP4
Download video MP3
Similar videos
-
 0:47
0:47
hashing and eke - applied cryptography
-
 0:50
0:50
eke authentication solution - applied cryptography
-
 2:23
2:23
cryptographic hash function solution - applied cryptography
-
 1:59
1:59
hash chain solution - applied cryptography
-
 1:34
1:34
hash collision solution - applied cryptography
-
 7:08
7:08
what is a cryptographic hashing function? (example purpose)
-
 11:42
11:42
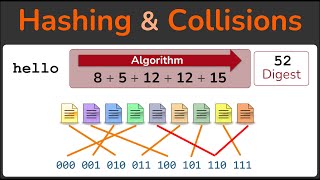
hashing, hashing algorithms, and collisions - cryptography - practical tls
-
 11:33
11:33
cryptography: hashing
-
 0:26
0:26
eke authentication - applied cryptography
-
 3:28
3:28
cryptographic hash function - applied cryptography
-
 0:36
0:36
double hash solution - applied cryptography
-
 1:12
1:12
eke authentication implementation solution - applied cryptography
-
 0:34
0:34
oaep solution - applied cryptography
-
 0:44
0:44
wire labels solution - applied cryptography
-
 1:42
1:42
weak collision resistance solution - applied cryptography
-
 0:59
0:59
prove a vote solution - applied cryptography
-
 0:49
0:49
know about encryption and hashing #encryption #hashing #cybersecurity #encoding #decoding #sna
-
 1:26
1:26
hash chain - applied cryptography
-
 0:13
0:13
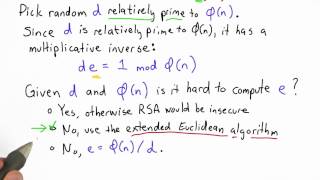
compute e solution - applied cryptography
-
 0:25
0:25
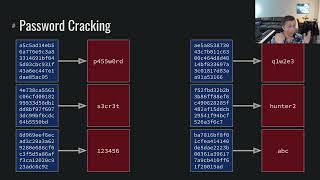
salted password scheme solution - applied cryptography