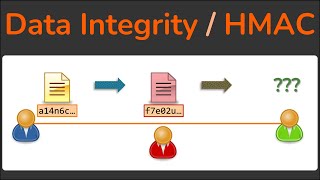
hmac & message authentication codes (macs) - why hashing alone is not enough for data integrity
Published 11 months ago • 675 plays • Length 6:09Download video MP4
Download video MP3
Similar videos
-
 7:24
7:24
data integrity - how hashing is used to ensure data isn't modified - hmac - cryptography
-
 6:33
6:33
hmac explained | keyed hash message authentication code
-
 2:20
2:20
hash based message authentication
-
 1:21
1:21
16. message authentication code mac
-
 8:43
8:43
hashed message authentication code hmac
-
 8:40
8:40
secret key exchange (diffie-hellman) - computerphile
-
 1:15:07
1:15:07
lecture 22: mac (message authentication codes) and hmac by christof paar
-
 7:28
7:28
passwords & hash functions (simply explained)
-
 9:53
9:53
integrity - hash vs mac
-
 9:24
9:24
securing stream ciphers (hmac) - computerphile
-
 9:45
9:45
what is hashing? | what is hashing with example | hashing explained simply | simplilearn
-
 7:13
7:13
#35 mac ( message authentication code ) - working and significance |cns|
-
 7:40
7:40
mac based on hash function | hmac in network security
-
 11:48
11:48
understanding hashing sha-1 and hmac - data security
-
 8:10
8:10
#36 hmac (hash based) & cmac (cipher based) |cns|
-
 2:09
2:09
diffrerence between hash function and mac | hash function vs message authentication code
-
 7:45
7:45
hash, mac & hmac
-
 16:47
16:47
cryptography: message integrity
-
 29:42
29:42
message authentication code (mac) and hmac - cryptography - cyber security cse4003
-
 21:56
21:56
authenticating data with message authentication codes
-
 11:26
11:26
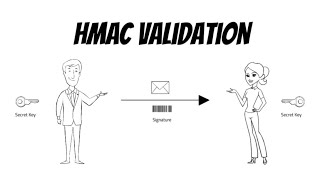
cryptography basics: hmac validation