data integrity - how hashing is used to ensure data isn't modified - hmac - cryptography
Published 2 years ago • 51K plays • Length 7:24Download video MP4
Download video MP3
Similar videos
-
 6:33
6:33
hmac explained | keyed hash message authentication code
-
 6:09
6:09
hmac & message authentication codes (macs) - why hashing alone is not enough for data integrity
-
 9:45
9:45
what is hashing? | what is hashing with example | hashing explained simply | simplilearn
-
 7:05
7:05
hmac - cryptography i
-
 11:42
11:42
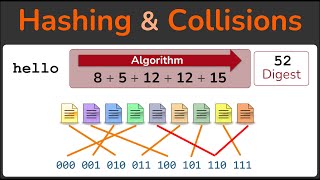
hashing, hashing algorithms, and collisions - cryptography - practical tls
-
 8:12
8:12
hashing algorithms and security - computerphile
-
 17:24
17:24
hmac using python
-
 18:23
18:23
lecture 4: hashing in-depth
-
 7:40
7:40
mac based on hash function | hmac in network security
-
 1:21
1:21
16. message authentication code mac
-
 8:43
8:43
hashed message authentication code hmac
-
 16:47
16:47
cryptography: message integrity
-
 5:15
5:15
how do ssl & tls protect your data? - confidentiality, integrity, authentication - practical tls
-
 4:12
4:12
keyed-hash message authentication code (hmac)
-
 7:17
7:17
data integrity and hash function